4 min read
How to Remove Malware & Clean a Hacked WordPress Site

WordPress sites have experienced a dramatic increase in malware infections during COVID-19. As a consequence, fixing a compromised website is now more crucial than ever. Since harmful software can entirely destroy your website after it has been hacked, it is important to act quickly to remove malware from your WordPress site.
WordPress’s variety of themes and plugins, which enable nearly anything to be done, has made it one of the most popular tools used globally when establishing a web page.
Security on WordPress sites is a very serious matter. Anyone can become a victim of hacking, and following guidelines will assist you in removing malware and cleaning up hacked WordPress sites, and limiting potential damage.
Ways to Remove Malware and Clean a Hacked WordPress Site
Different techniques detect and get rid of malware from a WordPress website. The most important point of threat protection is prevention, so we must take safety measures and steps to secure our website and remove malware from WordPress sites.
The key precaution WordPress users should take is to make sure their website is always upgraded to the most recent version available. New versions of WordPress typically solve common security flaws discovered in older versions. Additionally, removing any plugins we don’t use is important and performing the same action with the ones we do use.
Also Read: Useful Hacks And Customizations For Your BuddyPress Powered Website Via Reign Theme
1. Run a Computer Antivirus Scan- Remove Malware
Using an antivirus program that we have installed on our computer is another choice we have for finding files that have been contaminated. Using an FTP tool, we may download the complete website and then analyze every file that makes up the web to look for dangerous code.
The antivirus can typically examine the files while they are downloading, so once the download is complete, we should only check the report that has been prepared to find out which files have been identified as possibly dangerous.
Also Read: WordPress Security Plugins, For Keeping Your Site safe
2. Locate Malicious Users- Remove Malware
Some cybercriminals create accounts on your WordPress site and run malicious scripts to take advantage of any weakness in their theme or plugin.
3. Reduce Logins in WordPress by Locking WP Login
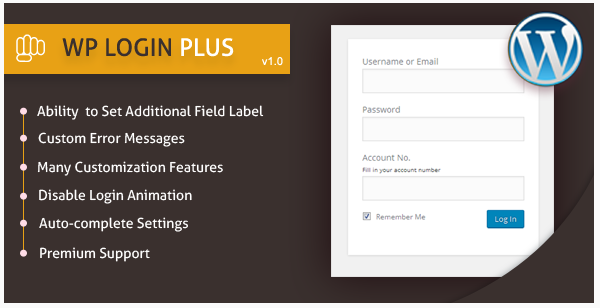
You can test as many login/password combinations as you wish to access your WordPress administration by default. Log in Every time a WordPress login attempt fails; LockDown logs the IP address and the timestamp. The login function is blocked if a predetermined number of unsuccessful attempts are discovered within a short period of time from the same IP range. This aids in guarding against brute force password discovery and protecting WordPress from such attacks.
Also Read: Free WordPress Login Page Security Plugins To Protect Your Site From Hackers
4. Gather Files by Date Of Modification
One of the quickest ways to detect potentially dangerous files is by using FTP to access files and categorizing them by modification date. People who have just gone through a change will therefore arrive first.
If we haven’t changed them, this might indicate that the problem is with some internal code. The problem with this method is that you must look through every folder that is a part of the website to find every infected file, which may be a very time-consuming operation if the code has been introduced in many files.
If you’re absolutely sure your website has been hacked, you can take the following actions to clean a hacked WordPress Site:
Also Read: WordPress Blog Portfolio Themes
5. Use a reliable hosting provider

If you are using shared hosting, your host should be your first port of inquiry because they might be aware of a bigger problem. Most of the time, your host might be able to take care of the problem for you, saving you a lot of time and effort. For this purpose, you can use a reliable hosting provider such as the seedbox app hosting by gigarapid.
Also Read: Marketing Hacks That Make a Difference
6. Recover Data from a Backup

Restoring to that point may work if you have a backup of your website from before it was hacked via your server or a specialized backup service like Jetpack Backup.
The problem can continue even after the site has been restored if the attack occurred in files that were not included in the backup.
Core Files for WordPress
If the impacted files are core WordPress files, you can remove any code that doesn’t belong there by comparing the code to a fresh download from WordPress.org.
Reinstalling WordPress from scratch is an additional choice to make sure all essential files are clean. You can accomplish that by selecting “Re-install now” under Dashboard > Updates. Although it may sound terrifying, this will only change the essential WordPress files and not your content, media, themes, or plugins.
Also Read: 11 WordPress Security Plugin To Secure Your Website
Conclusion of Remove Malware
As you may have noticed, restoring a WordPress site that has been hacked and infected with harmful code is not too difficult.
It is possible that the infection went a step further and infiltrated the code database. The recovery process in this instance is more challenging since all the tables must be searched for specific patterns that are employed as malicious code.
It is also true that sometimes these techniques might not provide a thorough cleaning and that you might need to use additional weapons and a magnifying glass to look deeper to identify the issue.
Updated on March 14, 2026
How To Create A Runner’s Community Website?
The Ten Most Important Web Design Advice for Your Website
Top Nine Computer Programming Languages To Learn
Choose A Web Hosting Service For Your Marketplace - Full Guide
Related reading
