6 min read
Sucuri Can Help You Fix Your Hacked WordPress Site

Whenever you think of Content Management Systems (CMS), you think of WordPress. And that is so because this website and blogging platform are so efficiently fast and it almost rules over 25 percent of the market share. All large and small organizations seem to be totally relying on WordPress, but they must also be aware of the security compromises that may take place.
Many a time, site owners or site administrators may choose to overlook the warning signals that tell that there is probably a red-alert kind of situation with the site. This can happen when site owners are not very well aware of the fact that the security aspects of a site have to be updated at regular intervals and that losing/manipulating site data can cause a significant blow to their business.

Let us have a look at the common indicators that tell us if the site has been hacked or not.
- Google, Bing, McAfee playing blacklist warnings
- The Browser starts to behave weirdly or abnormally
- If there is Spam in search engine content
- The website host notifies about your site suspension
- Core integrity issues or changes in the content/structure of files
- SEO poisoning: Warnings in Google search results
Now, if you happen to find out that your website has been hacked, keep reading on. We will tell you about Sucuri security plugin which is a security offering from the Sucuri website security stack. Let’s know more about how Sucuri can help.
Installing the Sucuri Plugin
- Log in to WordPress as an admin and go to Plugins > Add New.
- Type Sucuri Scanner into the field.
- Click Install Now next to Sucuri Security - Auditing, Malware Scanner and Security Hardening.
- Activate the plugin.
Site Scan
Scan your site to find malicious payloads and malware locations. Here’s how you can do it.
- Log into WordPress as an admin and go to Sucuri Security > Malware Scan.
- Click Scan Website.strong>
- If the site is infected, you will see a warning like this screenshot below.
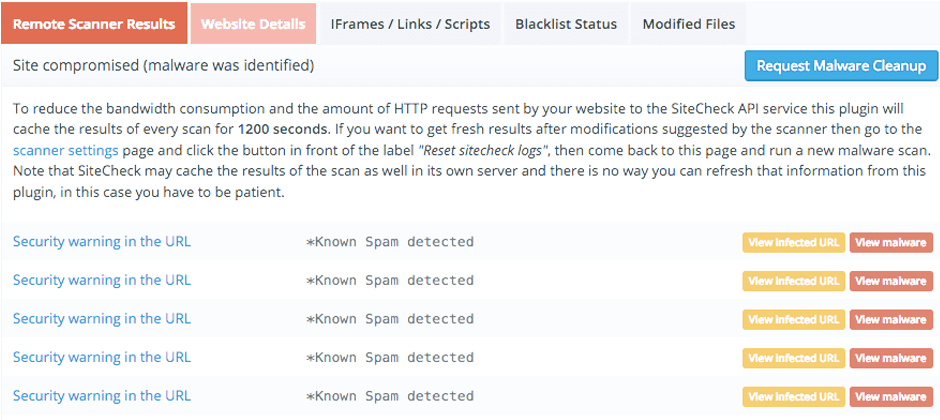
You can continue with other tests in this section if the remote scanner isn’t able to find any malware issues. If you want to, you can also manually review the iFrames / Links / Scripts tab of the Malware Scan to look for any suspicious component. You are required to scan all the websites if you run all of them on the same server in order to keep a check on cross-site contamination. You can also isolate your isolate hosting and web accounts, which is advisable.
The integrity of the Core File
The Sucuri security plugin checks for integrity issues in the wp-admin, wp-includes, and root folders to see if any of the core WordPress files have been modified. Our plugin checks for integrity issues in the wp-admin, wp-includes, and root folders. In order to carry out this step, follow these steps.
- Log in to WordPress as an admin
- Go to Sucuri Security > Dashboard
- Check the current status by reviewing the Core Integrity section
- If you see any modified, added, or removed files, this could be an indication of a hack.
- If all core files seem the same, your site is clean.
See if any Files were modified and also confirm User Logins
The Sucuri plugin can check the audit logs and identify if any modifications have been made. View the Audit Logs section for any unfamiliar recent changes in the last 7-30 days. If there is any, it’s a red flag. Also, check if any passwords were stolen or maliciously created. To do so, go to the Dashboard and see the list of users and the time they logged on. If you find any unusual activity, your site can be hacked.
Fix Your Hacked Site
Now that you are aware that your site is hacked, it is time to protect your core files and plugins. The Sucuri Security plugin now comes to your rescue. To remove a malware infection from your website database, use your database admin panel to connect to the database. You can also use tools like Search-Replace-DB or Adminer.
- Go to Sucuri Security > Dashboard and look for the review warnings under the Core Integrity section.
- Select Modified and Removed files and choose the Restore source action.
- Check the box to confirm ‘I understand that this operation cannot be reverted’. Click Proceed.
- Select Added files and choose the Delete file action. Repeat steps.
- Replace the custom files with fresh copies or with an uninfected recent backup.
- Remove unfamiliar users from your WordPress site. Have only one admin user and limit the privileges of other user roles.
- Log in to WordPress as an admin and go to Sucuri Security > Post-Hack.
- Reset the user passwords by clicking the ‘Reset User’s Password’ tab.
- Click Check the box next to the user account that you believe was compromised.
- Check the box to confirm I understand that this operation cannot be reverted.
- Click Reset User Password.
- The user will receive an email with a strong temporary password.
- Remove any left behind backdoors that are often embedded in files named similar to WordPress core files but located in the wrong directories. Backdoors commonly include the following PHP functions.
- Move_uploaded_file
- Remove Malware Warnings
Update WordPress Software and Reset Configuration Settings
After you have fixed your hack issues, request a review from Google, McAfee, Yandex, etc. (if they have blacklisted you). The review process can take several days. Now, update your WordPress software and if the Sucuri plugin identified other outdated software on your server (i.e., Apache, cPanel, PHP) you should update this as well to ensure that there are no security patches missing. Now change passwords for all access points such as user accounts, FTP/SFTP, SSH, cPanel, and your database. To do so, Log in to WordPress as an admin and go to Sucuri Security > Post-Hack.
Once the passwords are reset, force all users to log off using the Sucuri plugin. Force active users off by resetting your WordPress secret keys. To generate new secret keys,
- Log in to WordPress as an admin and go to Sucuri Security > Post-Hack.
- Click on Security Keys.
- Click Generate New Security Keys. This will force all users out of the WordPress dashboard.
Reinstall all plugins after a hack to ensure they are functional and free of residual malware. If you have deactivated plugins we recommend you remove them from your web server. Note that premium plugins will need to be reinstalled manually as their code is not available in the official WordPress repository.
- Log in to WordPress as an admin and go to Sucuri Security > Post-Hack.
- Go to the Reset Plugins tab.
- Select the plugins you want to reset (it is recommended to select them all).
- Click Process selected items.
Strengthen website security through Sucuri’s hardening
- Log in to WordPress as an admin and go to Sucuri Security > Hardening.
- Review the options to understand what they do.
- Click the Harden button to apply recommendations.
- Review the WordPress Codex if you want to research additional hardening methods. See the Website Firewall section below for more information about how we offer virtual patching and hardening.
Backups your Site
Here are some tips to help you with website backups:
- Store WordPress backups in an off-site location.
- Opt for run automatic backup frequency.
- Store your backups in multiple locations (cloud storage, your computer, external hard drives).
- Try restoring once to ensure that your website is functioning correctly.
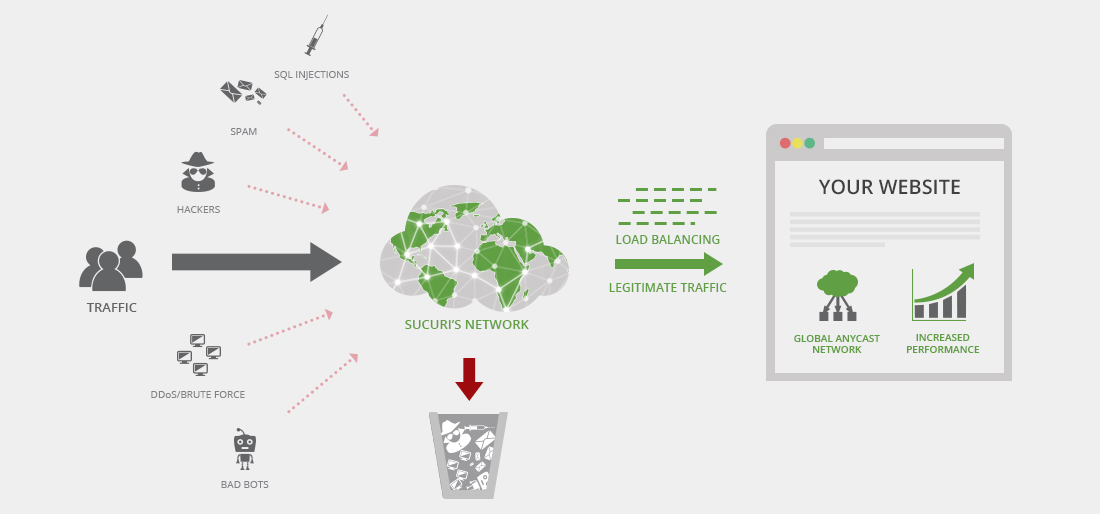
Run a scan and set up Sucuri website Firewall
You can opt for paid antivirus services such as BitDefender, Kaspersky, Sophos, F-Secure. For a free one, Malwarebytes, Avast, Microsoft Security Essentials and Avira are good options. Finally set up a Website Firewall to prevent a future hack and block Brute Force Attack. You can also go for the Sucuri Firewall. And simply connect it to the WordPress plugin using the Firewall (WAF) tab of the Sucuri plugin.
Related reading
